Blog Layout
Nearly 40% of Firms Fired Staff for Security Policy Breaches
Leo Daniels • August 20, 2020
This is a subtitle for your new post
Almost two-fifths (39%) of British business decision-makers have sacked employees because they breached corporate security policy during the pandemic.
The IAM specialist polled 200 UK respondents to find out more about how COVID-19 and mass remote working has impacted corporate cybersecurity.
Over half (58%) of respondents admitted that employees are more likely to try and bypass enterprise security practices when working from home.
That may explain why nearly two-thirds (65%) said they had made major changes to their cybersecurity policy to take account of their newly distributed workforce.
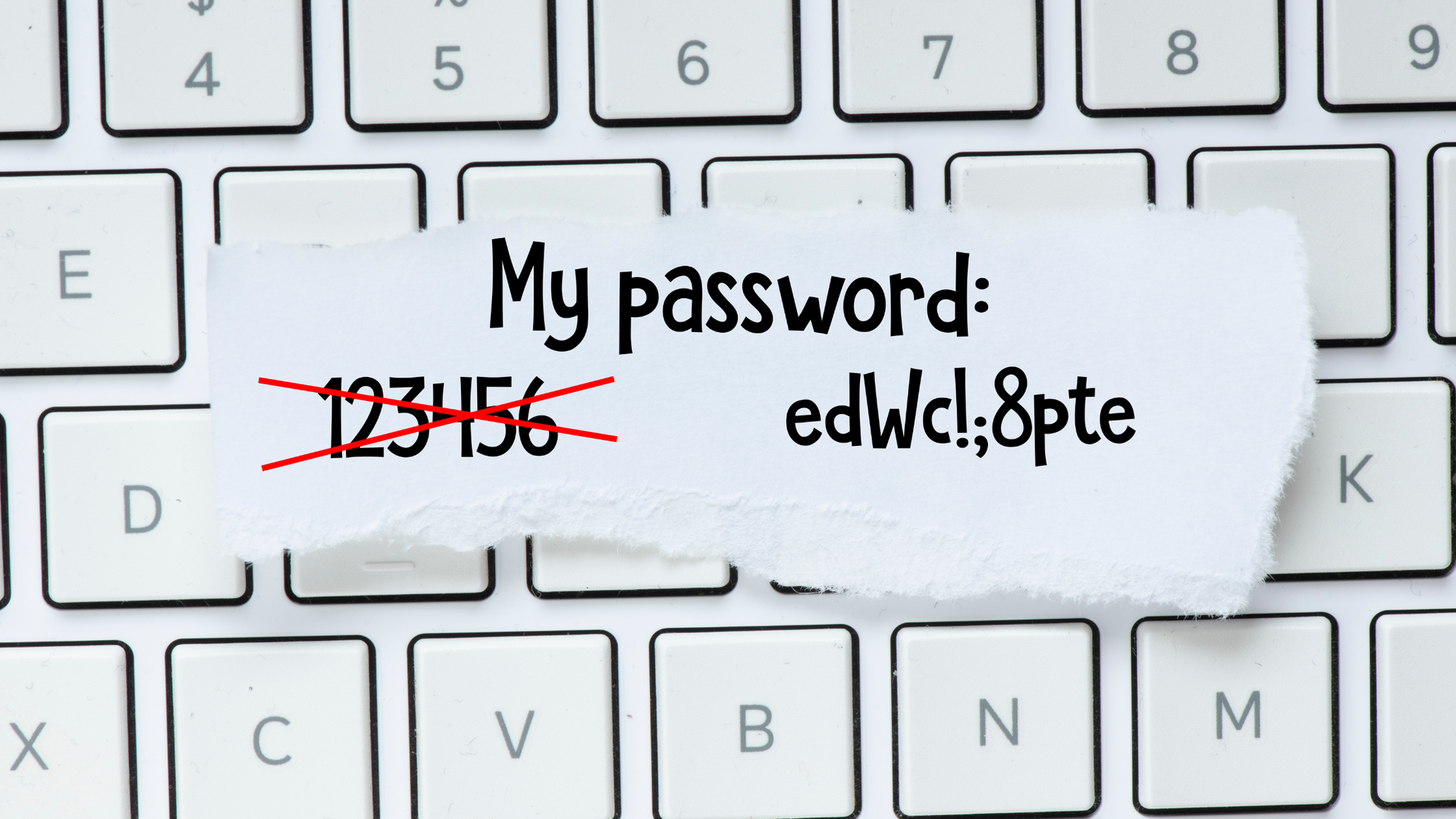
Changes to policy could include updates to remote access and authentication, which 57% of business decision makers said they are currently trying to implement. Multi-factor authentication (MFA) is regarded as industry best practice in helping to mitigate the risk of phishing and brute force attacks on RDP and corporate user accounts, for example.
A further 55% of respondents told Centrify that they are planning to formally ban staff from using personal devices to work from home.
This could also help to reduce cybersecurity risk as personal IT kit might be less well secured than corporate equivalents, and potentially used by other members of the household who may engage in risky online behaviour.
Centrify VP, Andy Heather, argued that humans continue to be the weakest link in the corporate security chain.
“With more people than ever working from home and left to their own devices, it’s inevitable that some will find security workarounds, such as using personal laptops and not changing passwords, in order to maximize productivity,” he added.
“It’s also possible that the changes in security procedures are not being communicated well to employees, and many are practicing unsafe internet usage without even realizing.”
We’re 1-fix, we can help you secure your business
At 1-fix, we take a realistic approach to technology – ensuring our client’s systems are best protected.
If you have any concerns, questions or simply want to explore how to better secure your business, please do get in touch with the team for a FREE demonstration, consultation to explore how exposed your business might be and identify actions to take.
Join Our Mailing List
Thank you for contacting us.
We will get back to you as soon as possible.
We will get back to you as soon as possible.
Oops, there was an error sending your message.
Please try again later.
Please try again later.
All sign-ups are handled inline with our privacy policy and can unsubscribe at any time.
Recent Blogs

By Craig Atkins
•
February 3, 2025
Businesses are constantly faced with decisions about how to best manage their IT infrastructure. One of the most significant choices is whether to adopt cloud services or stick with on-premises solutions. Both options have their advantages and drawbacks, and the right choice depends on your business's specific needs and goals. Let's explore the key differences between cloud services and on-premises solutions to help you make an informed decision.
Get in Touch
Fill in this form to contact us and we'll get back to you ASAP (same working day where possible):
Contact Us
Thank you for contacting us.
We will get back to you as soon as possible.
Oops, there was an error sending your message.
Please try again later.
1-Fix Limited
Company Registration Number: 06543233
Office Address:
1-Fix Limited
Office 240, Access Business Centre, willoughby Road, Bracknell, RG12 8FB
Registered Address:
1-Fix Limited
10 Beech Court, Wokingham Road, Hurst, Berkshire, RG10 0RQ