Blog Layout
Spotify Resets Passwords After Leaking User Data to Partners
Chris Lunn • January 6, 2021
This is a subtitle for your new post
Spotify has been forced to issue a password reset for users after admitting that their information was exposed to some of the firm’s third-party business partners.
The music streaming giant said in a customer data breach notification sent to the California attorney general that the privacy snafu was only discovered and fixed after seven months.
“On Thursday November 12, Spotify discovered a vulnerability in our system that inadvertently exposed your Spotify account registration information, which may have included email address, your preferred display name, password, gender, and date of birth only to certain business partners of Spotify,” it explained.
“Spotify did not make this information publicly accessible. We estimate that this vulnerability existed as of April 9, 2020 until we discovered it on November 12, 2020, when we took immediate steps to correct it.”
Spotify said it has contacted all of those partners to ensure they delete the exposed customer information, and has reset the passwords of affected users.
“We have no reason to believe that any unauthorized use of your information has or will occur, however, we urge you to change the passwords of all other online accounts for which you use the same email address and password,” it added.
This is the third security incident affecting the firm in recent months. A few days ago a hacktivist calling themselves ‘Daniel’ hijacked the Spotify for Artists page, posting messages in support of Taylor Swift and Donald Trump.
A few days before that, in late November, security researchers discovered a leaky cloud database containing logins for up to 350,000 Spotify users likely to have been part of a credential stuffing campaign.
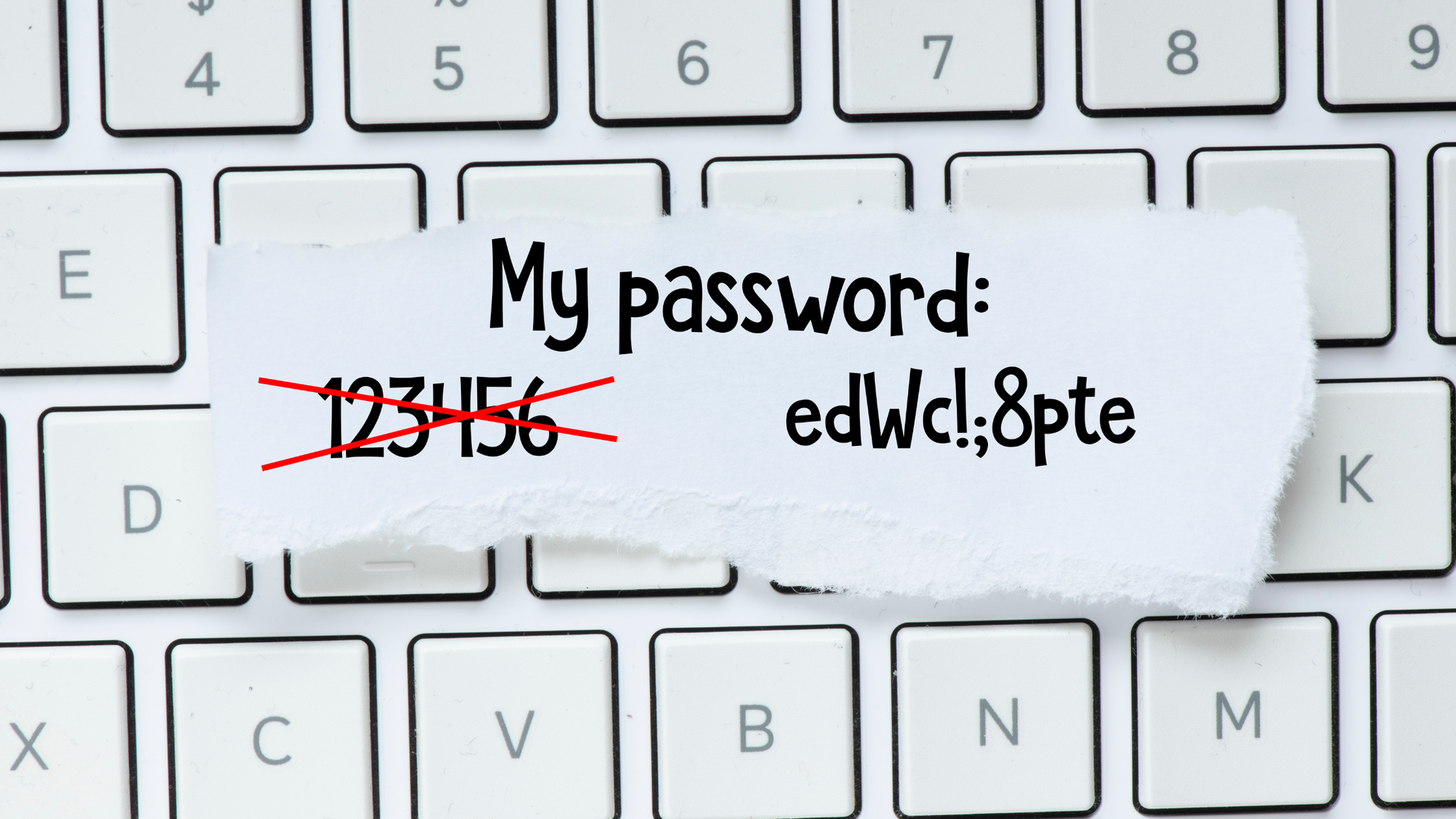
Laurence Pitt, technical security lead at Juniper Networks, urged internet users to use a password manager to help them store strong, unique credentials for each online account.
“Many people pay for premium Spotify services and with access to a password, anyone would be able to redirect a subscription for their own use,” he added.
“Password re-use is dangerous because if any of the data from this exposure does fall into the wrong hands, then it will end up in brute-force attack databases providing valid username/password combinations for access to other services.”
We’re 1-fix, we can help you secure your business
At 1-fix, we take a realistic approach to technology – ensuring our client’s systems are best protected.
If you have any concerns, questions or simply want to explore how to better secure your business, please do get in touch with the team for a FREE demonstration, consultation to explore how exposed your business might be and identify actions to take.
Join Our Mailing List
Thank you for contacting us.
We will get back to you as soon as possible.
We will get back to you as soon as possible.
Oops, there was an error sending your message.
Please try again later.
Please try again later.
All sign-ups are handled inline with our privacy policy and can unsubscribe at any time.
Recent Blogs

By Craig Atkins
•
February 3, 2025
Businesses are constantly faced with decisions about how to best manage their IT infrastructure. One of the most significant choices is whether to adopt cloud services or stick with on-premises solutions. Both options have their advantages and drawbacks, and the right choice depends on your business's specific needs and goals. Let's explore the key differences between cloud services and on-premises solutions to help you make an informed decision.

By Grant Taylor-Davis
•
January 23, 2025
One of the most effective ways to protect your organisation from cyber threats is through Security Awareness Training. But what exactly is Security Awareness Training, how does it work, and why is it essential for your business? Let's explore these questions with a focus on KnowBe4, a leading platform in this field.
Get in Touch
Fill in this form to contact us and we'll get back to you ASAP (same working day where possible):
Contact Us
Thank you for contacting us.
We will get back to you as soon as possible.
Oops, there was an error sending your message.
Please try again later.
1-Fix Limited
Company Registration Number: 06543233
Registered address:
1-Fix Limited
1F02 Arena Business Centre, 100 Berkshire Place, Winnersh Triangle, Wokingham, Berkshire RG41 5RD