Single Sign On and its benefits to business - What is it?
As we all know, the modern age of work is a digital one – this has left IT teams with a lot to deal with, and most are facing constant challenges. Stress has always been a factor but, in the modern world, with the rapid rate that technology has advanced over recent years, it has become even worse. Cyber threats and cyber criminals are becoming normal occurrences for the average firm so it is no wonder that they simply cannot keep up with their duties as efficiently as they used to.
Single Sign On can take some of that strain off the shoulders of your IT team and allow them to concentrate on the more important tasks they must complete.
Single Sign On – What is it?
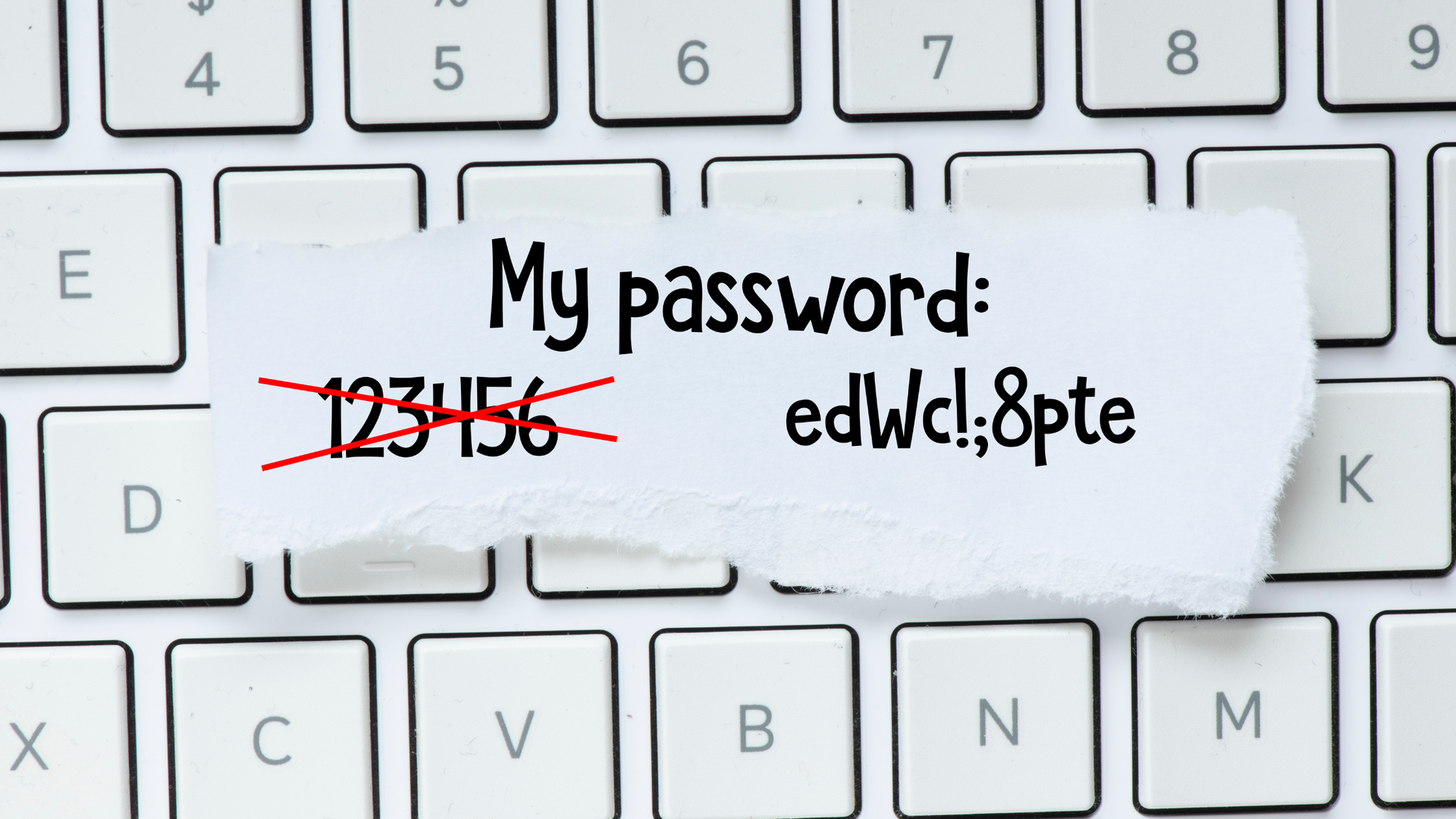
Single Sign On allows your users to log in to any related software system with a single username and password. This makes the process of logging in much easier, and the eventuality of forgotten passwords has become less common.
How does it work?
Once having already accessed a website using SSO, the user can then enter a different website that has the same relationship with the SSO solution, allowing the authentication flow to follow the same steps. Basically, this means that the system remembers that you got the password correct on the original site and, in turn, allows you access to the others.
A question that seems to be on everyone’s minds is ‘will it help me to be more secure?’. Let’s explore SSO further and find out, shall we?
Does it make my organisation more secure?
The majority of large businesses around the world give their team access to many applications (usually an average of around 15), and with these come the thousands of web apps available for your employees to sign up for as and when they like. The problem with this is that this is usually done without the IT Team’s knowledge. With the volume of apps on the market in the modern world reaching astonishing numbers, this has created further challenges for IT Teams around the globe, especially when you take into account all of their passwords and the variety of other tasks that they have to complete. We don’t envy them this task in the slightest - there must be guaranteed protection over the entire network and everything that resides on it - in particular, the sensitive data. Giving employees a way of using just one sign on (SSO) solves the IT problem of having to manage too many passwords.
Unfortunately, the features that make SSO so good are also the direct causes of its downfall. The ease of use it gives your employees (by allowing them to access apps with just one log-in) can also be passed to hackers. IT departments MUST have some sort of identity governance to make sure SSO is as secure as it can be. A lot of companies – to tackle this issue – adopt centralised identity authentication on special servers in order for them to act as ‘Gatekeepers’. So, when an employee signs in, their authentication passes through the SSO server which, in turn, passes on the credentials for authorising that person to use the app.
Many that have adopted SSO choose to also implement either two-factor or multi-factor authentication to make it as secure as it can be – both will improve security levels by a considerable amount, and both require your users to prove who they are through one or more additional authentication factors – this is all done before your SSO login.
By using these forms of identification (authentication) you put your system and, in turn, your organisation in good stead should a cyber criminal manage to obtain your SSO login.
Bringing ease to your IT team
Our team of specialists at 1-Fix offer an extensive range of business IT services - from desktop and server management to network design and cyber security assistance.
Our experts want to become vital members of your team and help you make a smooth beneficial transition to Cloud computing. In turn, this will boost the levels and quality of communication that your organisation is able to achieve. We can help you maintain a level of collaboration, communication, and productivity that can rival even the office setting, along with security that allows you to feel confident 100% of the time that you are not likely to be a victim of a cyber-attack.
Please do not hesitate to contact us to find out how we can help you.
Join Our Mailing List
We will get back to you as soon as possible.
Please try again later.
All sign-ups are handled inline with our privacy policy and can unsubscribe at any time.
Recent Blogs

Get in Touch
Fill in this form to contact us and we'll get back to you ASAP (same working day where possible):
Contact Us
Thank you for contacting us.
We will get back to you as soon as possible.
Oops, there was an error sending your message.
Please try again later.
1-Fix Limited
Company Registration Number: 06543233
Office Address:
1-Fix Limited
Office 240, Access Business Centre, Willoughby Road, Bracknell, RG12 8FB
Registered Address:
1-Fix Limited
10 Beech Court, Wokingham Road, Hurst, Berkshire, RG10 0RQ